Currently Empty: 0.00$
Curriculum
- 13 Sections
- 62 Lessons
- 2 Weeks
Expand all sectionsCollapse all sections
- Module 1 : Introduction to Network Security and Palo Alto Networks6
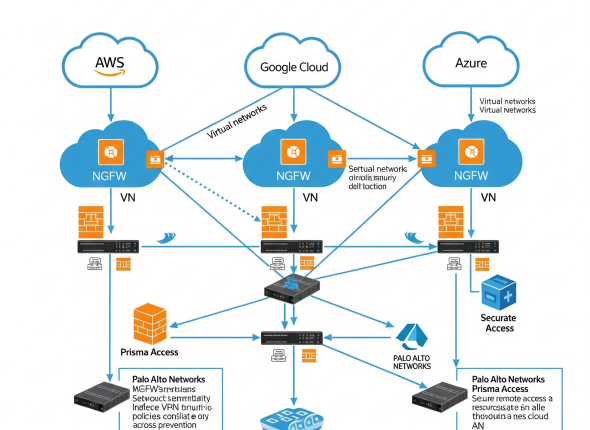
- Module 2 : Deploy Palo Alto Firewall in the Cloud Environment1
- Module 3 : Initial Configuration and Management5
- Module 4: Palo Alto Networks core features: App-ID, User-ID, Content-ID, Threat Prevention, and Dynamic Updates.6
- 4.1Key Concept of App-ID (Application Identification) and Layer 7 application
- 4.2Compare of Layer 4 and Layer 7 firewall rules and Custom APP-ID
- 4.3Overview of User-ID (User Identification)
- 4.4Content-ID (Content Inspection)
- 4.5Threat Prevention
- 4.6Overview of Dynamic Updates and Schedule Dynamic Updates
- Module 5 : Implementing Security Policy5
- 5.1Understanding Security Policy Rule Structure and Processing
- 5.2Configuring Firewall Rules: Source, Destination, Application, Service, Action
- 5.3Implementing NAT (Network Address Translation): Source NAT, Destination NAT
- 5.4Understanding and SSL/TLS Inspection and Implementing Decryption Policy
- 5.5Troubleshooting Security Policy Issues
- Module 6 : Implementing Security Profiles6
- 6.1Application Control: Visibility and Enforcement
- 6.2URL Filtering: Managing Web Access and Security
- 6.3Anti-Virus and Anti-Spyware: Protecting Against Malware
- 6.4Vulnerability Protection: Preventing Exploits
- 6.5File Blocking and Data Filtering
- 6.6WildFire Analysis: Understanding and Mitigating Advanced Threats
- Module 7 : Implementing Zone Protection Profile5
- 7.1Introduction to Zone Protection Profiles
- 7.2Configuring Flood Protection: SYN Flood, UDP Flood , ICMP Flood
- 7.3Configuring Reconnaissance Protection : TCP Port Scan, Host Sweep, UDP Port Scan, IP Protocol.
- 7.4Configuring Packet-Based Protection: IP Drop, TCP Drop, ICMP Drop and IP Option Drop
- 7.5Applying Zone Protection Profiles to Security Zones
- Module 8 : Denial-of-Service (DoS) Protection in Palo Alto Networks6
- Module 9 : VPN Configuration and Management3
- Module 10: Policy Optimization3
- Module 11 : Monitoring, Logging, and Reporting5
- Module 12 : Panorama – Centralized Network Security Management7
- Ready for Job Search4
To enroll in a course, you need to create an account on our platform, browse our course catalog, and click on the "Enroll" button next to the course you want to join. Follow the on-screen instructions to complete the registration process.
Yes, most of our courses offer a certificate of completion, provided you meet all the course requirements, such as passing quizzes and submitting assignments.
Courses often include quizzes, assignments, and sometimes final exams to assess your understanding of the material. The specific assessment methods will be detailed in the course syllabus.
Courses can be paid for using a credit/debit card, PayPal, or other payment methods specified at checkout. Payment is required at the time of enrollment.